How NexGenTek Compares to Traditional Cybersecurity Consulting
Most firms deliver assessments and recommendations. NexGenTek delivers secure operating systems.
Traditional cybersecurity consulting relies on audits, reports, and external recommendations. NexGenTek delivers similar capabilities through a structured system that integrates security architecture, execution, and ownership into a single model — reducing risk exposure, accelerating compliance, and lowering total cost without compromising enterprise standards.

How NexGenTek Compares to Traditional Cybersecurity Consulting
Most firms deliver assessments and recommendations. NexGenTek delivers secure operating systems.
Traditional cybersecurity consulting relies on audits, reports, and external recommendations. NexGenTek delivers similar capabilities through a structured system that integrates security architecture, execution, and ownership into a single model — reducing risk exposure, accelerating compliance, and lowering total cost without compromising enterprise standards.

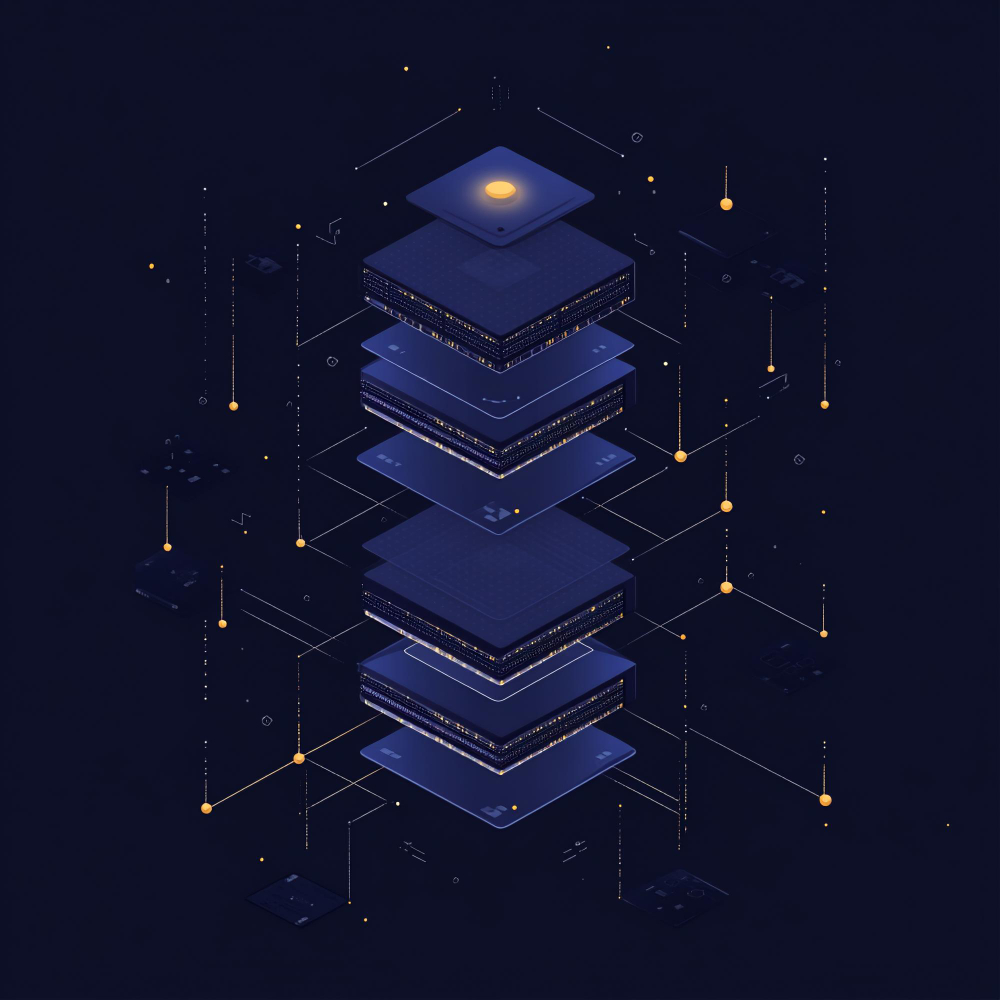
Security delivery structured for execution, control, and auditability.
Delivery models are extensions of the system, not separate offerings.
NexGenTek provides consulting expertise, execution teams, and augmentation within a single delivery model, eliminating the need for multiple vendors.
NexGenTek supports three engagement models for cybersecurity and risk. All three operate within the same governance framework, quality controls, and accountability structure. The system does not change. The scale does.

Full Security Program Delivery
End-to-end security program — risk assessment, architecture, implementation, compliance, and ongoing operations managed by NexGenTek under defined SLAs with full documentation transfer at close.
Ongoing Security Operations
Managed security operations embedded within client environment — NexGenTek operates SIEM, manages alerts, and maintains compliance evidence under a contractual SLA model.
Dedicated Security Teams
Specialist security engineers, compliance practitioners, and incident responders embedded within client operations — governed within the NexGenTek delivery framework.
Measured results — not projected
Outcomes are measured by operational security posture, not audit reports.
Prior program ran 18 months without reaching certification. 34 open findings, no continuous evidence collection, and no version-controlled policies. NexGenTek implemented gap remediation, SIEM deployment, and continuous evidence collection in one structured program. Certification-ready at week 14. Subsequent audit preparation reduced to 3 days — evidence available on demand, not assembled before each cycle.
Clinical operations across 8 facilities with HIPAA obligations and an ISO 27001 program that had never been independently audited. NexGenTek implemented the full ISO 27001 control set with continuous evidence generation. HIPAA Security Rule controls documented and evidenced from first deployment. No deficiencies in subsequent OCR review. Audit preparation now takes 3 business days across all facilities.
Organization had no documented incident response playbooks, no SIEM, and no defined escalation procedures. A ransomware event had taken 11 days to contain the previous year. NexGenTek deployed SIEM with custom detection rules, developed and tested IR playbooks across three tabletop exercises, and established 24/7 alert monitoring with a contractual P1 SLA. Subsequent event contained within 90 minutes — under SLA.
Built for enterprise procurement from day one.
Cybersecurity vendor procurement is the most scrutinized vendor risk assessment organizations conduct. NexGenTek is structured to meet every documentation requirement before any commercial commitment — not after a six-week exchange of questionnaires.
Compliance Package
Eight documents covering the complete vendor security review — delivered within 24 hours of NDA execution. No separate requests. No commercial agreement required before delivery.
Speak with our teamNDA within 2 hours · Package within 24h · No commitment required
- ISO 27001:2022 certificate + scope
- SOC 2 Type II full report (NDA)
- ISO 9001:2015 certificate
- Standard DPA (GDPR)
- Pre-completed SIG Lite questionnaire
- Penetration test executive summary
- BCP/DR plan executive summary
- SLA framework with service credit terms
Secure systems,
not isolated controls.
Build environments that are protected, governed, and operational by design. Security architecture, implementation, compliance, and ongoing operations — delivered as a single controlled system with defined outcomes and full documentation transfer at close.